TR-069
TR-069 (Technical Report 069) is a technical specification that defines an application layer protocol for remote management of end-user devices. It was published by the Broadband Forum and entitled CPE WAN Management Protocol (CWMP).
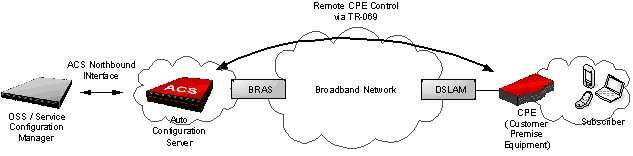
As a bidirectional SOAP/HTTP-based protocol, it provides the communication between customer-premises equipment (CPE) and Auto Configuration Servers (ACS). It includes both a safe auto configuration and the control of other CPE management functions within an integrated framework. The protocol addresses the growing number of different Internet access devices such as modems, routers, gateways, as well as end-user devices which connect to the Internet, such as set-top boxes, and VoIP-phones. The TR-069 standard was developed for automatic configuration and management of these devices by Auto Configuration Servers (ACS). The technical specifications are managed and published by the Broadband Forum. TR-069 was first published in May 2004, with amendments in 2006, 2007, 2010, July 2011 to version 1.3.[1] and November 2013 to version 1.4 (am5) [2]
Other forums, such as the Home Gateway Initiative (HGI), Digital Video Broadcasting (DVB) and WiMAX Forum endorsed CWMP as the protocol for remote management of home network devices and terminals (such as the DVB IPTV set-top box). There is a growing trend to add TR-069 management functionality to home networking devices behind the gateway, as well as many other access devices like M2M,[3] FTTH CPE/ONTs, WIMAX CPE[4] and other carrier access equipment.
Communication between the device and ACS
Transport details
CWMP is a text based protocol. Orders sent between the device (CPE) and auto configuration server (ACS) are transported over HTTP (or more frequently HTTPS). At this level (HTTP) CPE is behaving in the role of client and ACS in the role of HTTP server. This essentially means that control over the flow of the provisioning session is the sole responsibility of the device.
Provisioning session
All communications and operations are performed in the scope of the provisioning session. The session is always started by the device (CPE) and begins with the transmission of an Inform message. Its reception and readiness of the server for the session is indicated by an InformResponse message. That concludes the session initialization stage. The order of the next two stages depends on the value of the flag HoldRequests. If the value is false the initialization stage is followed by the transmission of device requests, otherwise ACS orders are transmitted first. The following description assumes the value is false.
In the second stage, orders are transmitted from the device to the ACS. Even though the protocol defines multiple methods that may be invoked by the device on the ACS, only one is commonly found - TransferComplete which is used to inform the ACS of the completion of a file transfer previously issued Download or Upload request. This stage is finalized by transmission of empty HTTP-request to the ACS.
In the third stage the roles change on the CWMP level. The HTTP-response for the empty HTTP-request by the device will contain a CWMP-request from the ACS. This will subsequently be followed by an HTTP-request containing a CWMP-response for the previous CWMP-request. Multiple orders may be transmitted one-by-one. This stage (and the whole provisioning session) is terminated by an empty HTTP-response from the ACS indicating that no more orders are pending.
Security and authentication
As vital data (like user names and passwords) may be transmitted to CPE via CWMP, it is essential to provide a secure transport channel and always authenticate the CPE against the ACS. Secure transport and authentication of the ACS identity can easily be provided by usage of HTTPS and verification of ACS certificate. Authentication of the CPE is more problematic. The identity of the device is verified based on a shared secret (password) at the HTTP level. Passwords may be negotiated between the parties (CPE-ACS) at every provisioning session. When the device contacts the ACS for the first time (or after a factory-reset) default passwords are used. In large networks it is the responsibility of the procurement to ensure each device is using unique credentials, their list is delivered with the devices themselves and secured.
Connection request
Because initialization and control of the provisioning session flow is the sole responsibility of the device, it is necessary for the ACS to be able to request a session start from the device. The connection request mechanism is also based on HTTP. In this case the device (CPE) is put in the role of HTTP-server. The ACS requests a connection from the device by visiting a negotiated URL and performing HTTP Authentication. A shared secret is also negotiated with the device in advance (e.g. previous provisioning session) to prevent the usage of CPEs for DDoS attacks on the provisioning server (ACS). After confirmation is sent by the device the provisioning session should be started as soon as possible and not later than 30 seconds after confirmation is transmitted.
Connection Request over NAT
The CWMP protocol also defines a mechanism for reaching the devices that are connected behind NAT (e.g. IP-Phones, Set-top boxes). This mechanism, based on STUN and UDP NAT traversal, is defined in document TR-069 Annex G (formerly in TR-111).
Amendment 5 of the protocol introduces alternative method of executing Connection Request via NAT based on XMPP (see Annex K of TR-069 Amendment 5 for details).
Data model
Most of the configuration and diagnostics is performed through setting and retrieving the value of the device parameters. These are organized in a well defined hierarchical structure that is more or less common to all device models and manufacturers. Broadband Forum publishes its data model standards in two formats - XML files containing a detailed specification of each subsequent data model and all of the changes between their versions and PDF files containing human-readable details. Supported standards and extensions should be clearly marked in the device data model. This should be in the field Device.DeviceSummary or InternetGatewayDevice.DeviceSummary which is required starting from Device:1.0 and InternetGatewayDevice:1.1 respectively. If the field is not found InternetGatewayDevice:1.0 is implied. As of Device:1.4 and InternetGatewayDevice:1.6 new field ( '<RO>'.SupportedDatamodel) for supported standard specification was introduced.
The model is always rooted in the single key named Device or InternetGatewayDevice depending on the manufacturer's choice. At each level of the structure objects and parameters (or array-instances) are allowed. Keys are constructed by concatenating the names of objects and parameter using '.'(dot) as a separator, e.g. InternetGatewayDevice.Time.NTPServer1 .
Each of the parameters may be marked as writable or non-writable. This is reported by the device in GetParameterNamesResponse message. The device should not permit the change of any parameter marked as read-only. Data model specifications and extensions clearly mark required status of most of the parameters.
Values applicable for the parameter, their type and meaning are also precisely defined by the standard.
Multi-instance objects
Some parts of the data model require the existence of multiple copies of the subtree. The best examples are those describing tables, e.g. Port Forwarding Table. An object representing an array will only have instance numbers or alias names as its children.
A multi-instance object may be writable (enabling dynamic creation and/or removal of its children) or read-only depending on the data represented. If for example the object represents four physical ports on a switch it should not be possible to add or remove them from the data model. If an instance is added to an object an identifier is assigned. After being assigned, identifiers may not change during the life-cycle of the device except for factory-reset.
Common problems
Even though the list of the parameters and their attributes is well-defined, most of the devices do not follow standards completely. Most common problems include missing parameters, omitted instance identifiers (for multi-instance objects where only one instance is present), wrong parameter access level and correctly using only defined valid values. For example, for the field that indicates supported standard of WLAN protocols, the value 'g' should indicate support of 802.11b and 802.11g, and 'g-only' support only of 802.11g. Even though values such as 'bg' or 'b/g' are not legal according to the Broadband Forum standards, they are very commonly found in device data models.
Common operations
The whole provisioning is built on top of a defined set of simple operations. Each order is considered atomic, though there is no support of transactions. If the device cannot fulfill the order a proper error needs to be returned to the ACS – the device should never break the provisioning session.
| Message | Description |
|---|---|
| GetParameterNames | Used to retrieve list of supported parameters from the device. |
| GetParameterValues | Retrieve current value of the parameters identified by keys. Could be used to retrieve one or multiple parameters at once. The version of the call with object as the key allows for retrieval of all of the parameters associated with that object |
| SetParameterValues | Sets the value of one or multiple parameters |
| GetParameterAttributes | Retrieves attributes of one or multiple parameters |
| SetParameterAttributes | Sets attributes of one or multiple parameters |
| Download | Orders CPE to download the file specified by URL and use it (depending on specified file type) as a Firmware Image, Configuration File, Ringer file, etc. |
| Upload | Orders CPE to upload specified file type to the specified destination. This could cover, for example, the current configuration file or log files. |
| AddObject | Adds new instance to an object |
| DeleteObject | Removes instance from an object |
High-level operations possible through TR-069
- Service activation and reconfiguration
- Initial configuration of the service as part of zero-touch or one-touch configuration process
- Service re-establishment (ex. after device is factory-reset, exchanged)
- Remote Subscriber Support
- Verification of the device status and functionality
- Manual reconfiguration
- Firmware and Configuration Management
- Firmware upgrade/downgrade
- Configuration backup/restore
- Diagnostics and monitoring
- Throughput (TR-143) and connectivity diagnostics
- Parameter value retrieval
- Log file retrieval
Security risks
The compromise of an ISP ACS server or the link between an ACS and CPE by unauthorized entities, including hackers and (domestic and foreign) government agencies, can give access to an entire ISP's subscriber base's routers (with TR-069 enabled). All the above-mentioned information and actions would be available to the potential attackers, including MAC addresses of all clients connected to the router, covert redirection of all DNS queries to a rogue DNS server, and even a surreptitious firmware update which may contain a backdoor to enable covert access from potentially anywhere in the world.[5] Through a recent study of TR-069 ACS implementations, Check Point's Malware and Vulnerability Research Group uncovered several flaws in solutions from ACS vendors, since some xSPs do not implement TR-069 ACS software in a secure manner.[6]
See also
References
- ↑ "CPE WAN Management Protocol" (PDF). TR-069 Amendment 4. Broadband Forum. July 2011. Retrieved February 16, 2012.
- ↑ "CPE WAN Management Protocol" (PDF). TR-069 Amendment 5. Broadband Forum. November 2013. Retrieved March 3, 2014.
- ↑ TR-069: Still Sexy After All These Years
- ↑ Architecture, detailed Protocols and Procedures WiMAX Device Reported Metrics & Diagnostics (DRMD) - Release 2
- ↑ Many home routers supplied by ISPs can be compromised en masse, researchers say
- ↑ Check Point's Malware and Vulnerability Research Group uncovered several flaws in solutions from ACS vendors
External links
- TR-069 Issue 1 Amendment 5 CPE WAN Management Protocol v1.4
- CPE WAN Management Protocol CWMP XML Schemas and Data Model Definitions
- Marketing Report TR-069 Deployment Scenarios, Issue: 1, August 2010
- TR-069 Protocol vs. SNMP Protocol
- TR-069 Knowledge Base TR-069 Knowledge Base