Signal (software)
|
Signal's icon for iOS and Chrome on the left, Android on the right | |
| Developer(s) | Open Whisper Systems and contributors |
|---|---|
| Initial release | July 2014[1] |
| Stable release |
Android 3.23.0 (November 28, 2016[2]) [±] |
| Preview release | Chrome app 0.26.0 (November 17, 2016[4]) [±] |
| Repository |
github |
| Development status | Active |
| Platform | |
| Available in | 31 languages |
| Type | Encrypted voice calling and instant messaging |
| License | |
| Website |
signal |
Signal is an encrypted instant messaging and voice calling application for Android and iOS. It uses the Internet to send one-to-one and group messages, which can include images and video messages, and make one-to-one voice calls. Signal uses standard cellular mobile numbers as identifiers and end-to-end encryption to secure all communications to other Signal users. The applications include mechanisms by which users can independently verify the identity of their messaging correspondents and the integrity of the data channel. In addition, a Chrome app that can link with a Signal client has been released.
Signal is developed by Open Whisper Systems. The clients are published as free and open-source software under the GPLv3 license. The server code is published under the AGPLv3 license.
History
Background (2010–2013)
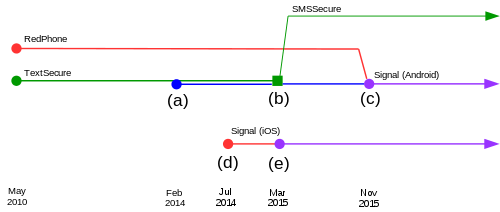
Signal is the successor of an encrypted voice calling app called RedPhone and an encrypted texting program called TextSecure. The beta versions of RedPhone and TextSecure were first launched in May 2010 by Whisper Systems,[9] a startup company co-founded by security researcher Moxie Marlinspike and roboticist Stuart Anderson.[10][11] Whisper Systems also produced a firewall and tools for encrypting other forms of data.[10][12] All of these were proprietary enterprise mobile security software and were only available for Android.
In November 2011, Whisper Systems announced that it had been acquired by Twitter. The financial terms of the deal were not disclosed by either company.[13] The acquisition was done "primarily so that Mr. Marlinspike could help the then-startup improve its security".[14] Shortly after the acquisition, Whisper Systems' RedPhone service was made unavailable.[15] Some criticized the removal, arguing that the software was "specifically targeted [to help] people under repressive regimes" and that it left people like the Egyptians in "a dangerous position" during the events of the 2011 Egyptian revolution.[16]
Twitter released TextSecure as free and open-source software under the GPLv3 license in December 2011.[10][17][18][19] RedPhone was also released under the same license in July 2012.[20] Marlinspike later left Twitter and founded Open Whisper Systems as a collaborative Open Source project for the continued development of TextSecure and RedPhone.[1][21]
Open Whisper Systems (2013–present)
Open Whisper Systems' website was launched in January 2013.[21]
In February 2014, Open Whisper Systems introduced the second version of their TextSecure Protocol (now Signal Protocol), which added end-to-end encrypted group chat and instant messaging capabilities to TextSecure.[22] Toward the end of July 2014, Open Whisper Systems announced plans to unify its RedPhone and TextSecure applications as Signal.[23] This announcement coincided with the initial release of Signal as a RedPhone counterpart for iOS. The developers said that their next steps would be to provide TextSecure instant messaging capabilities for iOS, unify the RedPhone and TextSecure applications on Android, and launch a web client.[23] Signal was the first iOS app to enable easy, strongly encrypted voice calls for free.[1][24] TextSecure compatibility was added to the iOS application in March 2015.[25][26]
From its launch in May 2010[9] until March 2015, the Android version of Signal (then called TextSecure) included support for encrypted SMS/MMS messaging.[27] From version 2.7.0 onward, the Android application only supported sending and receiving encrypted messages via the data channel.[28] Reasons for this included security flaws of SMS/MMS and problems with the key exchange.[28] Open Whisper Systems' abandonment of SMS/MMS encryption prompted some users to create a fork named Silence (initially called SMSSecure[29]) that is meant solely for the exchange of encrypted SMS and MMS messages.[30][31]
In November 2015, the TextSecure and RedPhone applications on Android were merged to become Signal for Android.[32] A month later, Open Whisper Systems announced Signal Desktop, a Chrome app that can link with a Signal client.[33] At launch, the app could only be linked with the Android version of Signal.[34] On September 26, 2016, Open Whisper Systems announced that Signal Desktop could now be linked with the iOS version of Signal as well.[35]
On October 4, 2016, the American Civil Liberties Union (ACLU) and Open Whisper Systems published a series of documents revealing that OWS had received a subpoena requiring them to provide information associated with two phone numbers for a federal grand jury investigation in the first half of 2016.[36][37][38] Only one of the two phone numbers was registered on Signal, and because of how the service is designed, OWS was only able to provide "the time the user’s account had been created and the last time it had connected to the service".[37][36] Along with the subpoena, OWS received a gag order requiring OWS not to tell anyone about the subpoena for one year.[36] OWS approached the ACLU, and they were able to lift part of the gag order after challenging it in court.[36] OWS said it was the first time they had received a subpoena, and that they were committed to treat "any future requests the same way".[38]
Features
Signal allows users to call other Signal users on iOS and Android. All calls are made over a Wi-Fi or data connection and with the exception of data fees are free of charge, including long distance and international.[24] Signal also allows users to send group, text, picture, and video messages over a Wi-Fi or data connection to other Signal users on iOS and on Android.
All communications to other Signal users are automatically end-to-end encrypted. The keys that are used to encrypt the user's communications are generated and stored at the endpoints (i.e. by users, not by servers).[39] Signal also has built-in mechanisms for verifying that no man-in-the-middle attack has occurred. For calls, Signal displays two words on the screen. If the words match on both ends of the call, the call is secure.[24][40] For messages, Signal users can compare key fingerprints (or scan QR codes) out-of-band.[41] The app employs a trust on first use mechanism in order to notify the user if a correspondent's key changes.[41]
On Android, users can opt into making Signal the default SMS/MMS application, allowing them to send and receive unencrypted SMS messages in addition to the standard end-to-end encrypted Signal messages.[22] Users can also opt into allowing Signal to fall back to unencrypted SMS/MMS when communicating with contacts who do not have Signal.[22]
The Android version of Signal allows the user to set a passphrase that encrypts the local message database and the user's encryption keys.[42] This does not encrypt the user's contact database or message timestamps.[42] The user can define a time period after which the application "forgets" the passphrase, providing an additional protection mechanism in case the phone is lost or stolen.[41] On iOS, the local message database is encrypted by the operating system if the user has a passphrase on their lock screen.
Signal also allows users to set timers to messages.[43] After a specified time interval, the messages will be deleted from both the sender's and the receivers' devices.[43] The time interval can be between five seconds and one week long,[43] and the timer begins for each recipient once they have read their copy of the message.[44] The developers have stressed that this is meant to be "a collaborative feature for conversations where all participants want to automate minimalist data hygiene, not for situations where your contact is your adversary".[43][44]
Limitations
Signal requires that the user has a phone number for verification.[45] The number does not have to be the same as on the device's SIM card; it can also be a VoIP number[45] or a landline as long as the user can receive the verification code and have a separate device to set up the software. A number can only be registered to one device at a time.[45]
Signal also requires that the primary device is an Android or iOS based smartphone with an Internet connection. A Chrome app that can link with a Signal client is in development.[34]
Android specific
Signal's official Android client requires the proprietary Google Play Services because the app is dependent on Google's GCM push messaging framework.[46] As of March 2015, Signal's message delivery has been done by Open Whisper Systems themselves and the client relies on GCM only for a wakeup event.[47]
In May 2016, Signal's lead developer Moxie Marlinspike requested that LibreSignal, a fork that had removed the GCM dependency, not use the Signal servers or the Signal name.[48] As a result, on 24 May 2016 the project README stated the project was "abandoned".[49]
Usability
In July 2016, the Internet Society published a user study that assessed the ability of Signal users to detect and deter man-in-the-middle attacks.[50] The study concluded that 21 out of 28 participants failed to correctly compare public key fingerprints in order to verify the identity of other Signal users, and that the majority of these users still believed they had succeeded while in reality they failed.[50]
Architecture
Encryption protocols
Signal instant messages are encrypted with the Signal Protocol (formerly known as the Axolotl protocol[51]). The protocol combines the Double Ratchet Algorithm, prekeys, and a 3-DH handshake.[52] It uses Curve25519, AES-256, and HMAC-SHA256 as primitives.[53] The protocol provides confidentiality, integrity, authentication, participant consistency, destination validation, forward secrecy, backward secrecy (aka future secrecy), causality preservation, message unlinkability, message repudiation, participation repudiation, and asynchronicity.[54] It does not provide anonymity preservation, and requires servers for the relaying of messages and storing of public key material.[54]
The Signal Protocol also supports end-to-end encrypted group chats. The group chat protocol is a combination of a pairwise double ratchet and multicast encryption.[54] In addition to the properties provided by the one-to-one protocol, the group chat protocol provides speaker consistency, out-of-order resilience, dropped message resilience, computational equality, trust equality, subgroup messaging, as well as contractible and expandable membership.[54]
In October 2014, researchers from Ruhr University Bochum published an analysis of the Signal Protocol.[53] Among other findings, they presented an unknown key-share attack on the protocol, but in general, they found that it was secure.[55]
As of October 2016, the Signal Protocol has also been implemented into WhatsApp, Facebook Messenger, and Google Allo, encrypting the conversations of "more than a billion people worldwide".[56]
Signal voice calls are encrypted with SRTP and the ZRTP key-agreement protocol, which was developed by Phil Zimmermann.[1][57]
Servers
Signal relies on centralized servers that are maintained by Open Whisper Systems. In addition to routing Signal's messages and calls, the servers also facilitate the discovery of contacts who are also registered Signal users and the automatic exchange of users' public keys. Open Whisper Systems has set up dozens of servers to handle the encrypted calls in more than 10 countries around the world to minimize latency.[1]
Contact discovery
The servers store registered users' phone numbers, public key material and push tokens which are necessary for setting up calls and transmitting messages.[58] In order to determine which contacts are also Signal users, cryptographic hashes of the user's contact numbers are periodically transmitted to the server.[59] The server then checks to see if those match any of the SHA256 hashes of registered users and tells the client if any matches are found.[59] The hashed numbers are thereafter discarded from the server.[58] Moxie Marlinspike has written that it is easy to calculate a map of all possible hash inputs to hash outputs and reverse the mapping because of the limited preimage space (the set of all possible hash inputs) of phone numbers, and that "practical privacy preserving contact discovery remains an unsolved problem".[60][59]
Metadata
All client-server communications are protected by TLS.[57][61] Once the server removes this layer of encryption, each message contains either the phone number of the sender or the receiver in plaintext.[60] This metadata could in theory allow the creation of "a detailed overview on when and with whom users communicated".[60] Signal's privacy policy states that these identifiers are only kept on the servers as long as necessary in order to place each call or transmit each message.[58] Open Whisper Systems have asserted that their servers do not keep logs about who called whom and when.[62] In June 2016, Marlinspike told The Intercept that "the closest piece of information to metadata that the Signal server stores is the last time each user connected to the server, and the precision of this information is reduced to the day, rather than the hour, minute, and second."[63]
The group messaging mechanism is designed so that the servers do not have access to the membership list, group title, or group icon.[28] Instead, the creation, updating, joining, and leaving of groups is done by the clients, which deliver pairwise messages to the participants in the same way that one-to-one messages are delivered.[64][65]
Federation
Signal's server architecture was federated between December 2013 and February 2016. In December 2013, it was announced that the messaging protocol that is used in Signal had successfully been integrated into the Android-based open-source operating system CyanogenMod.[66][67][68] Since CyanogenMod 11.0, the client logic was contained in a system app called WhisperPush. According to Open Whisper Systems, the Cyanogen team ran their own Signal messaging server for WhisperPush clients, which federated with Open Whisper Systems' Signal server, so that both clients could exchange messages with each-other.[68] The WhisperPush source code was available under the GPLv3 license.[69] In February 2016, the CyanogenMod team discontinued WhisperPush and recommended that its users switch to Signal.[70] In May 2016, Moxie Marlinspike wrote that federation with the CyanogenMod servers degraded the user experience and held back development, and that Open Whisper Systems' servers will probably not federate with other servers again.[48]
Licensing
The complete source code of the Signal clients for Android, iOS and Google Chrome are available on GitHub under a free software license.[5][6][7] This enables interested parties to examine the code and help the developers verify that everything is behaving as expected. It also allows advanced users to compile their own copies of the applications and compare them with the versions that are distributed by Open Whisper Systems. In March 2016, Moxie Marlinspike wrote that, apart from some shared libraries that aren't compiled with the project build due to a lack of Gradle NDK support, Signal for Android is reproducible.[71]
The software that handles Signal's message routing is called Signal-Server and it is also open source.[8] In January 2013, Moxie Marlinspike wrote that the server-side component of Signal's voice calling feature (formerly RedPhone) is a TURN server that acts as a bridge for the data connections that are required to establish calls between mobile devices.[72][73][74] In November 2016, a web developer questioned why Open Whisper Systems had not open sourced the server-side component of Signal's voice calling feature.[75] Open Whisper Systems has tweeted that there are "plenty of [open-source software] options to choose from".[76] Open Whisper Systems does not officially provide support for people to host their own servers.[77]
Distribution
Signal is officially distributed only through the Google Play store, Apple's App Store, and the Chrome Web Store. Applications distributed via Google Play are signed by the developer of the application, and the Android operating system checks that updates are signed with the same key, preventing others from distributing updates that the developer themselves did not sign.[78][79] The same applies to iOS applications that are distributed via Apple's App Store.[80]
Open Whisper Systems have declined requests to distribute the Android version of Signal as a separate APK package binary or through third-party distribution platforms. Signal's predecessor (TextSecure) was briefly included in the F-Droid software repository in 2012, but was removed at the developer's request because it was an unverified build and exceptionally out of date. Open Whisper Systems have subsequently said that they will not support their applications being distributed through F-Droid because it does not provide timely software updates, relies on a centralized trust model and necessitates allowing the installation of apps from unknown sources which harms Android's security for average users.[46] F-Droid subverts the other distribution platforms' decentralized trust model by often building and signing their own packages, meaning F-Droid administrators or anyone else with access could be compelled to push out malicious updates to any application.[78] Additionally, the keys for most applications in the main repository are stored on machines that are accessible from the Internet[81] (i.e. not separated by an air gap), which Marlinspike asserts is an unacceptable security risk.[82]
Reception
In October 2014, the Electronic Frontier Foundation (EFF) included Signal in their updated surveillance self-defense guide.[83] In November 2014, Signal received a perfect score on the EFF's secure messaging scorecard;[39] it received points for having communications encrypted in transit, having communications encrypted with keys the provider doesn't have access to (end-to-end encryption), making it possible for users to independently verify their correspondents' identities, having past communications secure if the keys are stolen (forward secrecy), having the code open to independent review (open source), having the security designs well-documented, and having a recent independent security audit.[39] At the time, "ChatSecure + Orbot", Pidgin (with OTR), Silent Phone, and Telegram's optional "secret chats" also received seven out of seven points on the scorecard.[39]
On December 28, 2014, Der Spiegel published slides from an internal NSA presentation dating to June 2012 in which the NSA deemed Signal's encrypted voice calling component (RedPhone) on its own as a "major threat" to its mission, and when used in conjunction with other privacy tools such as Cspace, Tor, Tails, and TrueCrypt was ranked as "catastrophic," leading to a "near-total loss/lack of insight to target communications, presence..."[84][85]
Former NSA contractor Edward Snowden has endorsed Signal on multiple occasions.[33] In his keynote speech at SXSW in March 2014, he praised Signal's predecessors (TextSecure and RedPhone) for their ease-of-use.[86] During an interview with The New Yorker in October 2014, he recommended using "anything from Moxie Marlinspike and Open Whisper Systems".[87] During a remote appearance at an event hosted by Ryerson University and Canadian Journalists for Free Expression in March 2015, Snowden said that Signal is "very good" and that he knew the security model.[88] Asked about encrypted messaging apps during a Reddit AMA in May 2015, he recommended Signal.[89][90] In November 2015, Snowden tweeted that he used Signal "every day".[32][91]
In September 2015, the American Civil Liberties Union called on officials at the U.S. Capitol to ensure that lawmakers and staff members have secure communications technology.[92] One of the applications that the ACLU recommended in their letter to the Senate Sergeant at Arms and to the House Sergeant at Arms was Signal, writing:
One of the most widely respected encrypted communication apps, Signal, from Open Whisper Systems, has received significant financial support from the U.S. government, has been audited by independent security experts, and is now widely used by computer security professionals, many of the top national security journalists, and public interest advocates. Indeed, members of the ACLU’s own legal department regularly use Signal to make encrypted telephone calls.[93]
Following the 2016 Democratic National Committee email leak, Vanity Fair reported that Marc Elias, the general counsel for Hillary Clinton's presidential campaign, had instructed DNC staffers to exclusively use Signal when saying anything "remotely contentious or disparaging" about Republican presidential nominee, Donald Trump.[94][95]
Developers and funding
Signal is developed by a nonprofit software group called Open Whisper Systems.[96] The group is funded by a combination of donations and grants, and all of its products are published as free and open-source software.
As of October 2016, the project has received an unknown amount of donations from individual sponsors via the Freedom of the Press Foundation.[97] Open Whisper Systems has received grants from the Knight Foundation,[98] the Shuttleworth Foundation,[99] and the Open Technology Fund,[100] a U.S. government funded program that has also supported other privacy projects like the anonymity software Tor and the encrypted instant messaging app Cryptocat.
See also
- Comparison of instant messaging clients
- Comparison of VoIP software
- Internet privacy
- Secure communication
References
- 1 2 3 4 5 Greenberg, Andy (29 July 2014). "Your iPhone Can Finally Make Free, Encrypted Calls". Wired. Retrieved 18 January 2015.
- ↑ Open Whisper Systems (28 November 2016). "Signal – Private Messenger". Google Play. Google. Retrieved 1 December 2016.
- ↑ Open Whisper Systems (30 November 2016). "Signal - Private Messenger". App Store. Apple. Retrieved 1 December 2016.
- ↑ Open Whisper Systems (17 November 2016). "Signal Private Messenger". Chrome Web Store. Google. Retrieved 1 December 2016.
- 1 2 Open Whisper Systems. "Signal-iOS". GitHub. Retrieved 14 January 2015.
- 1 2 Open Whisper Systems. "Signal-Android". GitHub. Retrieved 5 November 2015.
- 1 2 Open Whisper Systems. "Signal-Desktop". GitHub. Retrieved 7 April 2016.
- 1 2 Open Whisper Systems. "Signal-Server". GitHub. Retrieved 21 November 2016.
- 1 2 "Announcing the public beta". Whisper Systems. 25 May 2010. Archived from the original on 30 May 2010. Retrieved 22 January 2015.
- 1 2 3 Garling, Caleb (20 December 2011). "Twitter Open Sources Its Android Moxie | Wired Enterprise". Wired. Retrieved 21 December 2011.
- ↑ "Company Overview of Whisper Systems Inc.". Bloomberg Businessweek. Retrieved 2014-03-04.
- ↑ Greenberg, Andy (2010-05-25). "Android App Aims to Allow Wiretap-Proof Cell Phone Calls". Forbes. Retrieved 2014-02-28.
- ↑ Cheredar, Tom (28 November 2011). "Twitter acquires Android security startup Whisper Systems". VentureBeat. Retrieved 2011-12-21.
- ↑ Yadron, Danny (9 July 2015). "Moxie Marlinspike: The Coder Who Encrypted Your Texts". The Wall Street Journal. Retrieved 10 July 2015.
- ↑ Greenberg, Andy (2011-11-28). "Twitter Acquires Moxie Marlinspike's Encryption Startup Whisper Systems". Forbes. Retrieved 2011-12-21.
- ↑ Garling, Caleb (28 November 2011). "Twitter Buys Some Middle East Moxie | Wired Enterprise". Wired. Retrieved 21 December 2011.
- ↑ Aniszczyk, Chris (20 December 2011). "The Whispers Are True". The Twitter Developer Blog. Twitter. Archived from the original on 24 October 2014. Retrieved 22 January 2015.
- ↑ "TextSecure is now Open Source!". Whisper Systems. 20 December 2011. Archived from the original on 6 January 2012. Retrieved 22 January 2015.
- ↑ Pachal, Pete (2011-12-20). "Twitter Takes TextSecure, Texting App for Dissidents, Open Source". Mashable. Retrieved 2014-03-01.
- ↑ "RedPhone is now Open Source!". Whisper Systems. 18 July 2012. Archived from the original on 31 July 2012. Retrieved 22 January 2015.
- 1 2 "A New Home". Open Whisper Systems. 2013-01-21. Retrieved 2014-03-01.
- 1 2 3 Donohue, Brian (24 February 2014). "TextSecure Sheds SMS in Latest Version". Threatpost. Retrieved 14 July 2016.
- 1 2 Mimoso, Michael (29 July 2014). "New Signal App Brings Encrypted Calling to iPhone". Threatpost.
- 1 2 3 Evans, Jon (29 July 2014). "Talk Private To Me: Free, Worldwide, Encrypted Voice Calls With Signal For iPhone". TechCrunch. AOL.
- ↑ Lee, Micah (2015-03-02). "You Should Really Consider Installing Signal, an Encrypted Messaging App for iPhone". The Intercept. Retrieved 2015-03-03.
- ↑ Geuss, Megan (2015-03-03). "Now you can easily send (free!) encrypted messages between Android, iOS". Ars Technica. Retrieved 2015-03-03.
- ↑ Open Whisper Systems (6 March 2015). "Saying goodbye to encrypted SMS/MMS". Retrieved 24 March 2016.
- 1 2 3 Rottermanner et al. 2015, p. 3
- ↑ BastienLQ (20 April 2016). "Change the name of SMSSecure". GitHub (pull request). SilenceIM. Retrieved 27 August 2016.
- ↑ "TextSecure-Fork bringt SMS-Verschlüsselung zurück". Heise (in German). 2 April 2015. Retrieved 29 July 2015.
- ↑ "SMSSecure: TextSecure-Abspaltung belebt SMS-Verschlüsselung wieder". Der Standard (in German). 3 April 2015. Retrieved 1 August 2015.
- 1 2 Greenberg, Andy (2 November 2015). "Signal, the Snowden-Approved Crypto App, Comes to Android". Wired. Condé Nast. Retrieved 19 March 2016.
- 1 2 Franceschi-Bicchierai, Lorenzo (2 December 2015). "Snowden's Favorite Chat App Is Coming to Your Computer". Motherboard. Vice Media LLC. Retrieved 4 December 2015.
- 1 2 Coldewey, Devin (7 April 2016). "Now's your chance to try Signal's desktop Chrome app". TechCrunch. AOL Inc. Retrieved 5 May 2016.
- ↑ Marlinspike, Moxie (26 September 2016). "Desktop support comes to Signal for iPhone". Open Whisper Systems. Retrieved 26 September 2016.
- 1 2 3 4 Perlroth, Nicole; Benner, Katie (4 October 2016). "Subpoenas and Gag Orders Show Government Overreach, Tech Companies Argue". The New York Times. The New York Times Company. Retrieved 4 October 2016.
- 1 2 Kaufman, Brett Max (4 October 2016). "New Documents Reveal Government Effort to Impose Secrecy on Encryption Company" (Blog post). American Civil Liberties Union. Retrieved 4 October 2016.
- 1 2 "Grand jury subpoena for Signal user data, Eastern District of Virginia". Open Whisper Systems. 4 October 2016. Retrieved 4 October 2016.
- 1 2 3 4 "Secure Messaging Scorecard. Which apps and tools actually keep your messages safe?". Electronic Frontier Foundation. 4 November 2014.
- ↑ "Exactly how does Zfone and ZRTP protect against a man-in-the-middle (MiTM) attack?". The Zfone Project. Retrieved 25 January 2015.
- 1 2 3 Rottermanner et al. 2015, p. 5
- 1 2 Rottermanner et al. 2015, p. 9
- 1 2 3 4 Greenberg, Andy (11 October 2016). "Signal, the Cypherpunk App of Choice, Adds Disappearing Messages". Wired. Condé Nast. Retrieved 11 October 2016.
- 1 2 Marlinspike, Moxie (11 October 2016). "Disappearing messages for Signal". Open Whisper Systems. Retrieved 11 October 2016.
- 1 2 3 Kolenkina, Masha (20 November 2015). "Will any phone number work? How do I get a verification number?". Open Whisper Systems. Retrieved 20 December 2015.
- 1 2 Kolenkina, Masha (25 February 2016). "Why do I need Google Play installed to use Signal? How can I get Signal APK?". Open Whisper Systems. Archived from the original on 2 April 2016. Retrieved 13 October 2016.
- ↑ Marlinspike, Moxie (6 March 2015). "Saying goodbye to encrypted SMS/MMS". Open Whisper Systems. Retrieved 20 December 2015.
- 1 2 Edge, Jake (18 May 2016). "The perils of federated protocols". LWN.net. Retrieved 5 July 2016.
- ↑ Le Bihan, Michel (24 May 2016). "README.md". GitHub. LibreSignal. Retrieved 6 November 2016.
- 1 2 Schröder et al. 2016
- ↑ Marlinspike, Moxie (30 March 2016). "Signal on the outside, Signal on the inside". Open Whisper Systems. Retrieved 9 April 2016.
- ↑ Unger et al. 2015, p. 241
- 1 2 Frosch et al. 2016
- 1 2 3 4 Unger et al. 2015, p. 239
- ↑ Pauli, Darren. "Auditors find encrypted chat client TextSecure is secure". The Register. Retrieved 4 November 2014.
- ↑ "Moxie Marlinspike - 40 under 40". Fortune. Time Inc. 2016. Retrieved 6 October 2016.
- 1 2 Marlinspike, Moxie (17 July 2012). "Encryption Protocols". GitHub. Archived from the original on 5 September 2015. Retrieved 8 January 2016.
- 1 2 3 "Privacy Policy". Open Whisper Systems. n.d. Retrieved 6 September 2016.
- 1 2 3 Moxie Marlinspike (3 January 2013). "The Difficulty Of Private Contact Discovery". Open Whisper Systems. Retrieved 14 January 2016.
- 1 2 3 Rottermanner et al. 2015, p. 4
- ↑ Frosch et al. 2016, p. 7
- ↑ Brandom, Russell (29 July 2014). "Signal brings painless encrypted calling to iOS". The Verge. Retrieved 26 January 2015.
- ↑ Lee, Micah (22 June 2016). "Battle of the Secure Messaging Apps: How Signal Beats WhatsApp". The Intercept. First Look Media. Retrieved 6 September 2016.
- ↑ Moxie Marlinspike (5 May 2014). "Private Group Messaging". Open Whisper Systems. Retrieved 2014-07-09.
- ↑ Moxie Marlinspike (24 February 2014). "The New TextSecure: Privacy Beyond SMS". Open Whisper Systems. Retrieved 26 February 2014.
- ↑ Andy Greenberg (2013-12-09). "Ten Million More Android Users' Text Messages Will Soon Be Encrypted By Default". Forbes. Retrieved 2014-02-28.
- ↑ Seth Schoen (2013-12-28). "2013 in Review: Encrypting the Web Takes A Huge Leap Forward". Electronic Frontier Foundation. Retrieved 2014-03-01.
- 1 2 Moxie Marlinspike (2013-12-09). "TextSecure, Now With 10 Million More Users". Open Whisper Systems. Retrieved 2014-02-28.
- ↑ CyanogenMod (Jan 7, 2014). "android_external_whispersystems_WhisperPush". GitHub. Retrieved Mar 26, 2015.
- ↑ Sinha, Robin (20 January 2016). "CyanogenMod to Shutter WhisperPush Messaging Service on February 1". Gadgets360. NDTV. Retrieved 23 January 2016.
- ↑ Marlinspike, Moxie (31 March 2016). "Reproducible Signal builds for Android". Open Whisper Systems. Retrieved 31 March 2016.
- ↑ Marlinspike, Moxie (31 January 2013). "Creating a low-latency calling network". Open Whisper Systems. Retrieved 12 November 2016.
- ↑ Marlinspike, Moxie (16 June 2013). "On P2P: It's not possible for...". Reddit. Retrieved 12 November 2016.
- ↑ Marlinspike, Moxie (14 June 2013). "P2P is not possible on mobile data...". Reddit. Retrieved 12 November 2016.
- ↑ Lomas, Natasha (7 November 2016). "Signal app-maker rebuts criticism of dev direction by calling for more community help". TechCrunch. AOL Inc. Retrieved 12 November 2016.
- ↑ Open Whisper Systems [whispersystems] (3 November 2016). "You mean a turn server? Plenty of oss options to choose from." (Tweet). Retrieved 12 November 2016 – via Twitter.
- ↑ Kolenkina, Masha (22 November 2015). "How can I host my own server?". Open Whisper Systems. Retrieved 6 July 2016.
- 1 2 Marlinspike, Moxie (12 February 2013). "moxie0 commented Feb 12, 2013". GitHub. Retrieved 13 October 2016.
- ↑ "Sign Your App". Android Studio. Google. Retrieved 13 October 2016.
- ↑ "About Code Signing". Apple Developer. Apple. 13 September 2016. Retrieved 13 October 2016.
- ↑ Marlinspike, Moxie (16 October 2013). "moxie0 commented Oct 16, 2013". GitHub. Retrieved 13 October 2016.
- ↑ Marlinspike, Moxie (21 October 2013). "moxie0 commented Oct 21, 2013". GitHub. Retrieved 13 October 2016.
- ↑ "Surveillance Self-Defense. Communicating with Others". Electronic Frontier Foundation. 2014-10-23.
- ↑ SPIEGEL Staff (28 December 2014). "Prying Eyes: Inside the NSA's War on Internet Security". Der Spiegel. Retrieved 23 January 2015.
- ↑ "Presentation from the SIGDEV Conference 2012 explaining which encryption protocols and techniques can be attacked and which not" (PDF). Der Spiegel. 28 December 2014. Retrieved 23 January 2015.
- ↑ Eddy, Max (11 March 2014). "Snowden to SXSW: Here's How To Keep The NSA Out Of Your Stuff". PC Magazine: SecurityWatch. Retrieved 2014-03-16.
- ↑ "The Virtual Interview: Edward Snowden - The New Yorker Festival". YouTube. The New Yorker. 11 October 2014. Retrieved 24 May 2015.
- ↑ Cameron, Dell (6 March 2015). "Edward Snowden tells you what encrypted messaging apps you should use". The Daily Dot. Retrieved 24 May 2015.
- ↑ Yuhas, Alan (21 May 2015). "NSA surveillance powers on the brink as pressure mounts on Senate bill – as it happened". The Guardian. Retrieved 24 May 2015.
- ↑ Beauchamp, Zack (21 May 2015). "The 9 best moments from Edward Snowden's Reddit Q&A". Vox Media. Retrieved 24 May 2015.
- ↑ Barrett, Brian (25 February 2016). "Apple Hires Lead Dev of Snowden's Favorite Messaging App". Wired. Condé Nast. Retrieved 2 March 2016.
- ↑ Nakashima, Ellen (22 September 2015). "ACLU calls for encryption on Capitol Hill". The Washington Post. Nash Holdings LLC. Retrieved 22 September 2015.
- ↑ Macleod-Ball, Michael W.; Rottman, Gabe; Soghoian, Christopher (22 September 2015). "The Civil Liberties Implications of Insecure Congressional Communications and the Need for Encryption" (PDF). Washington, DC: American Civil Liberties Union. pp. 5–6. Retrieved 22 September 2015.
- ↑ Bilton, Nick (26 August 2016). "How the Clinton Campaign Is Foiling the Kremlin". Vanity Fair. Condé Nast. Retrieved 1 September 2016.
- ↑ Blake, Andrew (27 August 2016). "Democrats warned to use encryption weeks before email leaks". The Washington Times. The Washington Times, LLC. Retrieved 1 September 2016.
- ↑ Franceschi-Bicchierai, Lorenzo (18 November 2014). "WhatsApp messages now have Snowden-approved encryption on Android". Mashable. Retrieved 23 January 2015.
- ↑ "Donate to Support Encryption Tools for Journalists". Freedom of the Press Foundation. Retrieved 17 October 2016.
- ↑ "TextSecure". Knight Foundation. Retrieved 5 January 2015.
- ↑ "Moxie Marlinspike". Shuttleworth Foundation. Retrieved 14 January 2015.
- ↑ "Open Whisper Systems". Open Technology Fund. Retrieved 26 December 2015.
Literature
- Frosch, Tilman; Mainka, Christian; Bader, Christoph; Bergsma, Florian; Schwenk, Jörg; Holz, Thorsten (March 2016). How Secure is TextSecure?. 2016 IEEE European Symposium on Security and Privacy (EuroS&P). Saarbrücken, Germany: IEEE. pp. 457–472. doi:10.1109/EuroSP.2016.41. ISBN 978-1-5090-1752-2. Retrieved 28 September 2016.
- Rottermanner, Christoph; Kieseberg, Peter; Huber, Markus; Schmiedecker, Martin; Schrittwieser, Sebastian (December 2015). Privacy and Data Protection in Smartphone Messengers (PDF). Proceedings of the 17th International Conference on Information Integration and Web-based Applications & Services (iiWAS2015). ACM International Conference Proceedings Series. ISBN 978-1-4503-3491-4. Retrieved 18 March 2016.
- Schröder, Svenja; Huber, Markus; Wind, David; Rottermanner, Christoph (18 July 2016). When Signal hits the Fan: On the Usability and Security of State-of-the-Art Secure Mobile Messaging (PDF). Proceedings of the 1st European Workshop on Usable Security (EuroUSEC ’16). Darmstadt, Germany: Internet Society (ISOC). ISBN 1-891562-45-2. Retrieved 29 August 2016.
- Unger, Nik; Dechand, Sergej; Bonneau, Joseph; Fahl, Sascha; Perl, Henning; Goldberg, Ian Avrum; Smith, Matthew (2015). SoK: Secure Messaging (PDF). Proceedings of the 2015 IEEE Symposium on Security and Privacy. IEEE Computer Society's Technical Committee on Security and Privacy. pp. 232–249. doi:10.1109/SP.2015.22.
External links
| Wikimedia Commons has media related to Open Whisper Systems. |
- Official website
- How to: Use Signal for Android by the Electronic Frontier Foundation
- How to: Use Signal on iOS by the Electronic Frontier Foundation