Open proxy
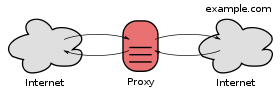
An open proxy is a proxy server that is accessible by any Internet user. Generally, a proxy server only allows users within a network group (i.e. a closed proxy) to store and forward Internet services such as DNS or web pages to reduce and control the bandwidth used by the group. With an open proxy, however, any user on the Internet is able to use this forwarding service.
Advantages
An anonymous open proxy is useful to those seeking online anonymity and privacy as it can help users hide their IP address from web servers since the server requests appear to originate from the proxy server. It makes it harder to reveal their identity and thereby helps preserve their perceived security while browsing the web or using other internet services. Real anonymity and extensive internet security might not be achieved by this measure alone as website operators can use client-side scripts to determine the browser’s real IP address and the open proxy may be keeping logs of all connections.
Disadvantages
It is possible for a computer to run as an open proxy server without the computer's owner knowing it. This can result from misconfiguration of proxy software running on the computer, or from infection with malware (viruses, trojans or worms) designed for this purpose.[1] If it is caused by malware, the infected computer is known as a zombie computer.
An open proxy is a high risk for the server operator:
- Such services are frequently used to break into foreign computer systems, child pornography is usually consumed through proxies, and illegal content is likely to be spread through such proxies.
- Such a proxy can cause a high bandwidth usage resulting in higher latency to the subnetwork and violation of bandwidth limits.
- A badly configured open proxy can also allow access to a private subnetwork or DMZ: this is a high security concern for any company or home network because computers that usually are out of risk or firewalled can be directly attacked.
Many open proxies run very slowly, sometimes below 14.4 kbit/s, or even below 300 bit/s, while other times the speed may change from fast to slow every minute.
Testing for access from an open proxy
Because open proxies are often implicated in abuse, a number of methods have been developed to detect them and to refuse service to them. IRC networks with strict usage policies automatically test client systems for known types of open proxies.[2] Likewise, a mail server may be configured to automatically test mail senders for open proxies, using software such as proxycheck.[3]
Groups of IRC and electronic mail operators run DNSBLs publishing lists of the IP addresses of known open proxies, such as AHBL, CBL, NJABL, and SORBS.
The ethics of automatically testing clients for open proxies are controversial. Some experts, such as Vernon Schryver, consider such testing to be "very bad form".[4] Others consider the client to have solicited the scan by connecting to a server whose terms of service include testing.
See also
- Open mail relay
- Open proxies blocked on Wikipedia
References
- ↑ "Accidental spamming, zombies and spoofing". Australian Communications and Media Authority. Retrieved 2015-12-08.
- ↑ "Blitzed Open Proxy Monitor". Blitzed.org. 2011-08-21. Retrieved June 21, 2014.
- ↑ "proxycheck: Open Proxy checker". Corpit.ru. Retrieved 2011-11-21.
- ↑ "localhost listed by njabl ?? - news.admin.net-abuse.email | Google Groups". Groups.google.com. 2003-12-12. Retrieved 2011-02-03.
two reasons why testing other people's systems for security holes is considered very bad form [...] It is impossible to know the motives of a tester. [...] Second, it offends people's territorial urges.
External links
| Wikimedia Commons has media related to Open proxies blocked on Wikimedia Commons. |
- Open proxies at DMOZ