Off-the-Record Messaging
Off-the-Record Messaging (OTR) is a cryptographic protocol that provides encryption for instant messaging conversations. OTR uses a combination of AES symmetric-key algorithm with 128 bits key length, the Diffie–Hellman key exchange with 1536 bits group size, and the SHA-1 hash function. In addition to authentication and encryption, OTR provides forward secrecy and malleable encryption.
The primary motivation behind the protocol was providing deniable authentication for the conversation participants while keeping conversations confidential, like a private conversation in real life, or off the record in journalism sourcing. This is in contrast with cryptography tools that produce output which can be later used as a verifiable record of the communication event and the identities of the participants. The initial introductory paper was named "Off-the-Record Communication, or, Why Not To Use PGP".[1]
The OTR protocol was designed by cryptographers Ian Goldberg and Nikita Borisov and released on 26 October 2004.[2] They provide a client library to facilitate support for instant messaging client developers who want to implement the protocol. A Pidgin and Kopete plugin exists that allows OTR to be used over any IM protocol supported by Pidgin or Kopete, offering an auto-detection feature that starts the OTR session with the buddies that have it enabled, without interfering with regular, unencrypted conversations.
History
OTR was presented in 2004 by Nikita Borisov, Ian Avrum Goldberg, and Eric A. Brewer as an improvement over the OpenPGP and the S/MIME system at the "Workshop on Privacy in the Electronic Society" (WPES).[1] The first version 0.8.0 of the reference implementation was published on November 21, 2004. In 2005 an analysis was presented by Mario Di Raimondo, Rosario Gennaro, and Hugo Krawczyk that called attention to several vulnerabilities and proposed appropriate fixes, most notably including a flaw in the key exchange.[3] As a result, version 2 of the OTR protocol was published in 2005 which implements a variation of the proposed modification that additionally hides the public keys. Moreover, the possibility to fragment OTR messages was introduced in order to deal with chat systems that have a limited message size, and a simpler method of verification against man-in-the-middle attacks was implemented.[4]
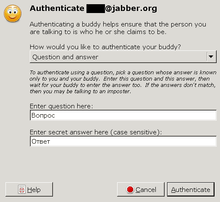
In 2007 Olivier Goffart published mod_otr[5] for ejabberd, making it possible to perform Man in the Middle attack on OTR users who don't check key fingerprints. OTR developers countered this attack by introducing socialist millionaire protocol implementation in libotr. Instead of comparing key checksums, knowledge of an arbitrary shared secret can be utilised for which relatively low entropy can be tolerated by using the socialist millionaire protocol.[6]
Version 3 of the protocol was published in 2012. As a measure against the repeated reestablishment of a session in case of several competing chat clients being signed on to the same user address at the same time, more precise identification labels for sending and receiving client instances were introduced in version 3. Moreover, an additional key is negotiated which can be used for another data channel.[7]
Several solutions have been proposed for supporting conversations with multiple participants. A method proposed in 2007 by Jiang Bian, Remzi Seker, and Umit Topaloglu uses the system of one participant as a "virtual server".[8] The method called "Multi-party Off-the-Record Messaging" (mpOTR) which was published in 2009 works without a central management host and was introduced in Cryptocat by Ian Goldberg et al.[9] In 2013, the Signal Protocol was introduced, which is based on OTR Messaging and the Silent Circle Instant Messaging Protocol (SCIMP). It brought about support for asynchronous communication ("offline messages") as its major new feature, as well as better resilience with distorted order of messages and simpler support for conversations with multiple participants.[10] OMEMO, introduced in an Android XMPP client called Conversations in 2015, integrates the Double Ratchet Algorithm used in Signal into the instant messaging protocol XMPP ("Jabber") and also enables encryption of file transfers. In the autumn of 2015 it was submitted to the XMPP Standards Foundation for standardisation.[11][12]
Implementation
In addition to providing encryption and authentication — features also provided by typical public-key cryptography suites, such as PGP, GnuPG, and X.509 (S/MIME) — OTR also offers some less common features:
- Forward secrecy: Messages are only encrypted with temporary per-message AES keys, negotiated using the Diffie-Hellman key exchange protocol. The compromise of any long-lived cryptographic keys does not compromise any previous conversations, even if an attacker is in possession of ciphertexts.
- Deniable authentication: Messages in a conversation do not have digital signatures, and after a conversation is complete, anyone is able to forge a message to appear to have come from one of the participants in the conversation, assuring that it is impossible to prove that a specific message came from a specific person. Within the conversation the recipient can be sure that a message is coming from the person they have identified.
Authentication
As of OTR 3.1, the protocol supports mutual authentication of users using a shared secret through the socialist millionaire protocol. This feature makes it possible for users to verify the identity of the remote party and avoid a man-in-the-middle attack without the inconvenience of manually comparing public key fingerprints through an outside channel.
Limitations
Due to limitations of the protocol, OTR does not support multi-user group chat as of 2009[13] but it may be implemented in the future. As of version 3[7] of the protocol specification, an extra symmetric key is derived during authenticated key exchanges that can be used for secure communication (e.g., encrypted file transfers) over a different channel. Support for encrypted audio or video is not planned. (SRTP with ZRTP exists for that purpose.) A project to produce a protocol for multi-party off-the-record messaging (mpOTR) has been organized by Cryptocat, eQualitie, and other contributors including Ian Goldberg.[9][14]
Since OTR protocol v3 (libotr 4.0.0) the plugin supports multiple OTR conversations with the same buddy who is logged in at multiple locations.[15]
Client support
| Developer(s) | OTR Development Team |
|---|---|
| Stable release |
4.1.1
/ 9 March 2016 |
| Development status | active |
| Written in | C |
| Operating system | Cross-platform |
| Type | Software Library |
| License | LGPL v2.1+[16] |
| Website | https://otr.cypherpunks.ca/index.php#downloads |
Native
These clients support Off-the-Record Messaging out of the box.
- Adium (OS X)
- Blink SIP client (OS X)
- BitlBee (cross-platform), since 3.0 (optional at compile-time)[17]
- CenterIM (Unix-like), since 4.22.2
- ChatSecure/Zom Mobile Messenger (Android, iOS)
- climm (Unix-like), since (mICQ) 0.5.4
- Conversations (Android)
- IronChat, based on Xabber (Android)
- Jitsi (cross-platform)
- Kadu (software) (cross-platform), since 1.0 [18]
- Kopete (Unix-like)[19][20]
- LeechCraft (cross-platform)[21][22]
- MCabber (Unix-like), since 0.9.4[23]
- Profanity, since 0.4.1
- Psi+ (cross-platform)[24][25]
- Textual 5 (OS X), since 5.1.2
- Xabber (Android)
Via plug-in
The following clients require a plug-in to use Off-the-Record Messaging.
- Gajim, with a third-party plugin[26][27] (no longer maintained and deprecated[28])
- irssi and xchat, with a third-party plugin[29]
- Miranda IM (Microsoft Windows), with a third-party plugin[30]
- Pidgin (cross-platform), with a plugin available from the OTR homepage[31]
- Psi (cross-platform), with a third-party plugin and build[32]
- Tkabber (cross-platform, since version 1.1), with a plugin from the Tkabber developers[33]
- WeeChat, with a third-party plugin[34]
Not in Google Talk
Although Gmail's Google Talk uses the term "off the record", the feature has no connection to the Off-the-Record Messaging protocol described in this article, its chats are not encrypted in the way described above - and could be logged internally by Google even if not accessible by end-users.[35][36]
References
- 1 2 Nikita Borisov, Ian Goldberg, Eric Brewer (2004-10-28). "Off-the-Record Communication, or, Why Not To Use PGP" (PDF). Workshop on Privacy in the Electronic Society. Retrieved 2014-03-06.
- ↑ Ian Goldberg (2014-10-26). [OTR-users] Happy 10th anniversary!. Retrieved 2015-04-27.
- ↑ Mario Di Raimondo; Rosario Gennaro; Hugo Krawczyk (2005). "Secure off-the-record messaging" (PDF). Proceedings of the 2005 ACM workshop on Privacy in the electronic society. Association for Computing Machinery: 81–89.
- ↑ "Off-the-Record Messaging Protocol version 2".
- ↑ "mod_otr".
- ↑ Chris Alexander; Ian Avrum Goldberg (February 2007). "Improved User Authentication in Off-The-Record Messaging" (PDF). Proceedings of the 2007 ACM workshop on Privacy in electronic society. New York: Association for Computing Machinery: 41–47. doi:10.1145/1314333.1314340.
- 1 2 "Off-the-Record Messaging Protocol version 3".
- ↑ Jiang Bian; Remzi Seker; Umit Topaloglu (2007). Off-the-Record Instant Messaging for Group Conversation (PDF). IEEE International Conference on Information Reuse and Integration. IEEE. doi:10.1109/IRI.2007.4296601.
- 1 2 Ian Avrum Goldberg; Berkant Ustaoğlu; Matthew D. Van Gundy; Hao Chen (2009). "Multi-party off-the-record messaging" (PDF). Proceedings of the 16th ACM Computer and Communications Security Conference. Association for Computing Machinery: 358–368. doi:10.1145/1653662.1653705.
- ↑ Nik Unger; Sergej Dechand; Joseph Bonneau; Sascha Fahl; Henning Perl; Ian Avrum Goldberg; Matthew Smith (2015). "SoK: Secure Messaging" (PDF). Proceedings of the 2015 IEEE Symposium on Security and Privacy. IEEE Computer Society's Technical Committee on Security and Privacy: 232–249.
- ↑ Straub, Andreas (25 October 2015). "OMEMO Encryption". XMPP Standards Foundation website. Retrieved 16 January 2016.
- ↑ Gultsch, Daniel (2 September 2015). "OMEMO Encrypted Jingle File Transfer". XMPP Standards Foundation website. Retrieved 16 January 2016.
- ↑ Ian Goldberg (May 27, 2009). "multi-party OTR communications? (and other OTR details)". OTR-users mailing list.
- ↑ Nadim Kobeissi (2014-02-01). "mpOTR Project Plan". Cryptocat wiki on GitHub.
- ↑ Ian Goldberg (September 4, 2012). "pidgin-otr and libotr 4.0.0 released!". OTR-announce mailing list.
- ↑ "Off-the-Record Messaging".
- ↑ "BitlBee Wiki". Wiki.bitlbee.org. 2014-01-25. Retrieved 2014-05-15.
- ↑ "Kadu 1.0 Release Notes".
- ↑ "kopete-otr in KDE for 4.1". Archived from the original on March 28, 2008.
- ↑ "kopete-otr review request".
- ↑ 0xd34df00d. "OTR Plugin". Github.com. Retrieved 2014-05-15.
- ↑ "Short description". Leechcraft.org. Retrieved 2014-05-15.
- ↑ "source code". MCabber.com. 2013-10-25. Retrieved 2014-05-15.
- ↑ "OTR Plugin". Github.com. Retrieved 2014-05-15.
- ↑ "Psi+ snapshots". Github.com. Retrieved 2014-05-15.
- ↑ "OTR plugin for Gajim".
- ↑ "Gajim Wiki".
- ↑ gajim-otr project: This software is experimental and potentially insecure. Do not rely on it
- ↑ "irssi-otr / xchat-otr plugin".
- ↑ "Miranda OTR Plugin".
- ↑ "OTR plugin for Pidgin".
- ↑ "Psi-Patches and OTR-Plugin on". Tfh-berlin.de. Retrieved 2014-05-15.
- ↑ "Tkabber OTR Plugin".
- ↑ "OTR plugin for WeeChat".
- ↑ "Chatting off the record - Talk Help".
- ↑ "Google Talk - Privacy Policy".
Further reading
- Joseph Bonneau; Andrew Morrison (2006-03-21). "Finite-State Security Analysis of OTR Version 2" (PDF). Retrieved 2013-09-05.
- Mario Di Raimondo; Rosario Gennaro & Hugo Krawczyk (2005). "Secure Off-the-Record Messaging" (PDF). Proceedings of the 2005 ACM Workshop on Privacy in the Electronic Society. Association for Computing Machinery. Retrieved 2013-08-27.
External links
- Official website
- Protocol specification
- Off-the-Record Messaging: Useful Security and Privacy for IM, talk by Ian Goldberg at the University of Waterloo (video)
- 'Off-the-Record' Instant Messaging Tutorial (encryption, authentication, deniability, ..) on YouTube